Trustus Scope
Securing Tenant, Cloud, and Domain
Trustus Foundational Trust across three frontiers of modern enterprise:
Boundary
Challenge
Privatized Access
Tenant (SaaS & Multi-Tenant)
Preventing tenant-based attacks and unauthorized access to environments like Microsoft 365, Salesforce, or custom clouds.
Trustus enforces cryptographic identity prior to the user hitting the native Identity Provider (IdP), serving as an unbreachable gate. Only trusted enterprise identities can attempt access, blocking unauthorized or personal accounts.
Cloud (AWS, Azure,
Google Cloud)
Protecting infrastructure management consoles, container environments, and APIs that are vulnerable to credential theft.
Trustus certificates enable secure machine-to-machine authentication (mTLS) and user-to-service access, eliminating human-readable secrets (passwords, access keys) for critical cloud infrastructure management.
Domain
(Web-Enabled Apps)
Securing all web-enabled applications and the private domain they reside on, without the complexity and risk of legacy VPNs.
The Trustus Privacy Bridge access gateway fronts the domain. It uses the foundational cryptographic identity
of the user and device to authorize the connection and secure access to internal web applications and the underlying private network resources.
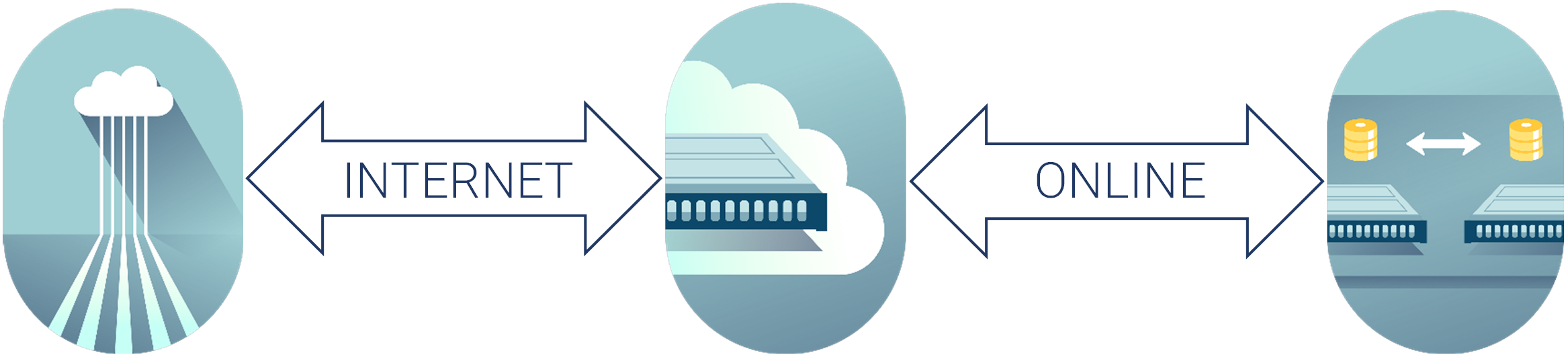
Universal Data Security
Consistent data protection, any environment.
Trustus Privacy Bridge ensures security
Staying in the public cloud, moving to hybrid/private, or on-prem, Trustus
delivers consistent protection for all data echelons. Our Privacy Bridge
authorizes only pre-validated, certificate-based device access.